|
Security (tagged articles)
The keyword Security is tagged in the following 56 articles.
2021, Vol. 13 No. 10
This paper assesses the political preferences and ideologies of the Trump administration and how they influenced framing issues in a way that has underestimated the threats of right-wing militia groups in the United States. President Trump and officials... Read Article »
2021, Vol. 13 No. 01
Israel has increased the nation’s Security presence around the Gaza Strip and in the West Bank. Here, the research project analyzes how transaction costs resulting from Israeli Security policy impact the output of manufacturing activities... Read Article »
2019, Vol. 11 No. 03
Radical thinking among the far-right is a growing Security problem for modern western society. Over the past several decades anti-government ideologies have been gaining legitimacy due to controversial interactions between Millennialist fringe religious... Read Article »
2019, Vol. 11 No. 02
In recent years, climate change has been increasingly framed as a Security issue, with some theorists going so far as to call it the most important Security issue of the 21st century. This paper will examine the relationship between climate change... Read Article »
2018, Vol. 10 No. 01
This paper analyzes the ongoing drug war being waged between Mexican drug trafficking organizations (DTOs), their rivals, and the U.S./Mexican governments. This analysis is conducted through the lens of drug control; namely, through an examination... Read Article »
2017, Vol. 9 No. 12
In 2010, over 250,000 Syrian farmers were forced from their land due to water shortages. Lack of water left these farmers dangerously food insecure, so they moved, en masse, into Syrian urban centers. This strained an already overburdened infrastructure... Read Article »
2017, Vol. 9 No. 11
South Sudan is the youngest and one of the most volatile nations in the world. After two decades of war, it gained its independence from Sudan in 2011. Peace, however, was short-lived. As oil prices plummeted and competition intensified, an ill-... Read Article »
2017, Vol. 10 No. 2
The global network of the Islamic State of Iraq and Syria (ISIS), also known as Daesh,2 is expanding rapidly. Southeast Asia is especially vulnerable because of its large Muslim population and its history of extremist groups. In fact, some experts... Read Article »
2017, Vol. 10 No. 2
For three decades prior to 9/11, West Germany fought its own war on terror. For 28 years, it faced off against the Red Army Faction (RAF), a small yet highly adaptable terrorist organization that constantly evolved to meet the countermeasures deployed... Read Article »
2017, Vol. 10 No. 2
In December 1948, the United Nations adopted the Universal Declaration of Human Rights, which recognized the universal human right to food. Most recently in July 2010, the U.N. General Assembly adopted resolution 64/292 that recognized the human... Read Article »
2016, Vol. 8 No. 11
In the early 1990s, two terrorist organizations, Hamas and the Fatah-led Palestinian Liberation Organization (PLO), were using terrorism to promote their political plight of Palestinian self-determination. Although both organizations vowed to use... Read Article »
2016, Vol. 2015/2016 No. 3
When Britain and France signed what became known as the ‘Entente Cordiale' in 1904, it brought into being an era of mutual cooperation between two neighbours whose past had often made them the best of enemies. The partnership served and survived... Read Article »
2016, Vol. 6 No. 2
Though somewhat counterintuitive given terrorist organizations' clandestine nature, such organizations do engage in strategic alliances and partnerships with one another. A handful of scholars have grappled with terrorist alliances, but a gap in... Read Article »
2016, Vol. 9 No. 2
Ambassador Paul Bremer of the Coalition Provisional Authority, America's interim government between Saddam's fall and the independent establishment of a new Iraqi government, issued two specific orders during his term which combined to create a... Read Article »
2016, Vol. 9 No. 2
Bataclan. San Bernadino. One need not read any further to understand how radicalization is crucial to counterterrorism and national Security. Some states have implemented counter-radicalization strategies to cull terrorism at its root. These tactics... Read Article »
2016, Vol. 2015/2016 No. 2
Cyber Security is a compelling problem for scholars of International Politics. Internet technology is so thoroughly integrated into civil society, commerce, governance, critical infrastructures, intelligence collection and law enforcement that the... Read Article »
2016, Vol. 2015/2016 No. 2
In Cyber War Will Not Take Place1, Thomas Rid develops his argument on the concept of "cyberwar", previously formulated in an article of the same name2 published in January 2012. His chief point is that "cyber war has never happened in the past,... Read Article »
2016, Vol. 2015/2016 No. 2
In June 2012, two years after the initial discovery of the Stuxnet worm,1 an excerpt from David Sanger's then soon to be released book entitled Confront and Conceal was published in the New York Times.2 This piece, purportedly based on the testimony... Read Article »
2016, Vol. 2015/2016 No. 2
Cyber Security is presented in the growing literature on the subject as an essentially "slippery" object for state Security.1 The Internet puts a lot of stress on the conventional conception of state Security as the insurance of the state's survival... Read Article »
2015, Vol. 7 No. 10
Considering information is the most valuable asset of any organization, information Security is one of the most important areas for every business and individual. Looking at the big picture, approximately 86% of all websites had a serious vulnerability... Read Article »
2015, Vol. 7 No. 02
This report examines the outcomes on various domains of development (cognitive, social emotional) of children with attachment disorders as well as internal working models of attachment, conditions of insecure attachment, information regarding Reactive... Read Article »
2014, Vol. 8 No. 1
This paper analyzes the grey market for cyber materials by evaluating the current nature of transactions within the market. This paper claims that vendors ought to be required to disclose information (to companies) on the vulnerabilities, exploits... Read Article »
2014, Vol. 8 No. 1
The formation and expansion of the U.S. Africa Command (USAFRICOM) signals the increasing strategic importance of Africa to U.S. Security interests, especially in light of the 2014 U.S.-Africa Leaders Summit on strategic relations. USAFRICOM is... Read Article »
2014, Vol. 8 No. 1
Legitimate whistleblower or traitor? While the public continues to debate which of these titles most aptly describes former National Security Agency (NSA) employee Edward Snowden, a movie set to start filming in January 2015 attests to the continuing... Read Article »
2014, Vol. 6 No. 03
Like the theories that explain it, group conflict has existed since man became a social creature. Nevertheless, social scientists remain frustrated in their attempts to explain ethnic conflict in any generalizable pattern. Social political theories... Read Article »
2014, Vol. 2013/2014 No. 1
There is a widespread belief that as societies and governments become increasingly reliant upon information technology, they in turn are becoming more vulnerable to a whole range of cyber-threats.1 Whether these dangers are capable of generating... Read Article »
2014, Vol. 2013/2014 No. 1
The concept of food Security is dynamic; it has been changing to incorporate new ideas over the years since it was established. In this piece, I will argue that if cultural acceptability is to be added as a tenant of food Security then so must sustainability... Read Article »
2014, Vol. 2013/2014 No. 1
IT is important to note th at the duty to cooperate, despite at times having been called a fundamental principle of international law2 has not been adequately defined.3 An expansive interpretation would be 'the duty to reach an agreement', which... Read Article »
2013, Vol. 4 No. 1
With nuclear proliferation a major threat to international Security, this study examines the factors that led three countries to denuclearize by applying Scott Sagan's three models: Security, domestic politics, and norms. Rather than only observing... Read Article »
2013, Vol. 7 No. 1
The current state of European strategic cooperation is optimistically described as "splintered" and pessimistically labeled as "nonexistent" by politicians and pundits alike. A potential retreat of the EU to staunch intergovernmentalism frustrates... Read Article »
2013, Vol. 5 No. 08
After World War II, the United States military gradually came into a position of overwhelming dominance in the world. Military spending in the United States far outpaces that of other countries, with their world share of military expenditures at... Read Article »
2013, Vol. 6 No. 2
Regionalism, as Edward Mansfield describes, usually involves policy coordination through formal institutions within a region.1 Although there are conceptual debates surrounding what a region is and what regionalism is, empirically speaking one would... Read Article »
2013, Vol. 5 No. 01
Everywhere, everyday we are reminded of the planetary crisis. Ice caps melt, forests are decimated, species go extinct and extreme climatic changes threaten the survival of human civilization. We desperately need a new narrative – a compelling... Read Article »
2012, Vol. 4 No. 12
While in many cases it serves as a stabilizing factor in the international system, and can even be called a force for good, international law cannot be considered “law” when applied to states or state action. To be considered “... Read Article »
2012, Vol. 4 No. 08
A public good is defined as a product or service that is both non-rival and non-excludable, meaning that one cannot withhold it from another without precluding all others from benefitting from it as well.[1] Examples of such products have come to... Read Article »
2012, Vol. 4 No. 04
Today, we live in the aftermath of the Internet revolution. Humanity has never before been more interconnected or had as much access to the same tools and information. As a driving force behind globalization and modern progress, the Internet enables... Read Article »
2012, Vol. 4 No. 03
The Internet is the world’s great equalizer. As the driving force behind globalization and modern progress, the Internet has enabled us to communicate with others across the world almost instantly and provides a medium for cultural, informational... Read Article »
2011, Vol. 3 No. 09
Since the early 1990s, rampant piracy off the coast of Somalia has become a major issue for global trade and Security, prompting strong responses from the international community. In 2010 alone, the collective cost of ransom money, military protection... Read Article »
2011, Vol. 3 No. 08
Somalia is home to roughly 9 million people, the overwhelming majority of whom are ethnic Somalis (UN Statistics Division 2010). The country has been plagued with conflict and disorder beginning just years after it attained independence. Following... Read Article »
2011, Vol. 4 No. 2
Recently, earthquakes in Haiti, Chile and New Zealand, mudslides in Brazil, a catastrophic oil spill in the Gulf of Mexico, the fallout from the fiscal crisis in Greece, and refugee flows out of Libya have highlighted the continued relevance of... Read Article »
2011, Vol. 3 No. 03
It is widely recognized that state Security is no longer contingent upon a balance of power or the threat of conquering states, but global stability is now instead jeopardized by weak or fragile states. Fragile states represent chaos, disorder,... Read Article »
2011, Vol. 3 No. 01
“Human Security means protecting vital freedoms. It means protecting people from critical and pervasive threats and situations, building on their strengths and aspirations. It also means creating systems that give people the building blocks... Read Article »
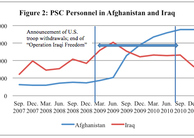
2010, Vol. 4 No. 1
Supporters of “green-badgers”—the nickname given to contractors working inside the American intelligence community—argue that after 9/11 the United States needed a more flexible labor pool of intelligence professionals to... Read Article »
2010, Vol. 2 No. 07
The United States presidency is a complex role, encompassing both domestic and foreign policy responsibilities. As a major world power, the United States has a large role in the realm of foreign policy, and it is the duty of the president to assume... Read Article »
2010, Vol. 2 No. 06
The Internet is a necessity in Americans’ lives and something that many access often throughout the day. Over 80% of students use one or more social networks and more than half log in at least once a day (Peluchette, 2008). The Internet &ldquo... Read Article »
2010, Vol. 2 No. 05
To understand an administration, you need to understand the key players. Through analyzing the Bush presidency, it is clear that the agenda was constructed and shaped by more than just one man. The President’s choice for executive cabinet... Read Article »
2010, Vol. 3 No. 2
Even before his inauguration, President Barack Obama made it clear that he believed torture was morally reprehensible and promised that under his administration the U.S. would no longer practice torture.1 Accordingly, on April 16th, 2009 Mr. Obama... Read Article »
2009, Vol. 1 No. 11
With the explosion of the use of the Internet for nearly all forms of negotiable instrument exchange, the constant transmission of time sensitive and vital corporate communications, and the ubiquitous presence of malicious software writers, verifying... Read Article »
2009, Vol. 1 No. 11
As the sophistication of cyber criminals continues to increase, their methods and targets have also evolved. Instead of building the large Internet worms that have become so familiar, these criminals are now spending more time concentrating on wealth... Read Article »
2009, Vol. 1 No. 11
Multiple undersea internet cables were mysteriously severed and subsequently gained significant attention in the beginning of 2008. The attacks on those cables highlighted the enormous amount of internet traffic that uses the undersea cable system... Read Article »
2009, Vol. 1 No. 11
The earliest form of cryptography was the simple writing of a message, as most people could not read (New World, 2007). In fact, the very word cryptography comes from the Greek words kryptos and graphein, which mean hidden and writing, respectively... Read Article »
2008, Vol. 1 No. 2
The United Nations Security Council is the most important organ in the United Nations, charged with determining “the existence of any threat to peace, breach of peace, or act of aggression” and to “maintain or restore international... Read Article »
1997, Vol. 1996/1997 No. 1
I have not seen Goldeneye (honest!) but I do remember a clip where James Bond is admonished as a “relic” for not being able to keep up with events after the Cold War. However the quote is interesting as regards the future for the... Read Article »
1997, Vol. 1996/1997 No. 1
The aim of this article is to assess the role of the Organisation of Security and Co-operation in Europe (OSCE) in the post-Cold War era. The paper will firstly give a brief outline of the development of the Conference on Security and Co-operation... Read Article »
1997, Vol. 1996/1997 No. 2
Threats to international Security may assume many guises all of which deserve thorough analysis. Indeed, as we approach the new millennium, there are a multitude of ‘morbid symptoms’ which threaten to thwart any attempts at achieving... Read Article »
1997, Vol. 1996/1997 No. 2
Nuclear weapons were first used in anger during the Second World War against the Japanese. The Horishima and Nagasaki experience left nobody in any doubt that nuclear weapons were unique. Never before had so much destruction been meted out so... Read Article »
Expedited Article Review
Submit an article and get a decision fast.
If you need a fast decision, INQUIRIES Journal offers expedited processing of your submission for a small fee. Depending on the expedited review option you choose, you can receive a decision in as few as 5-days.
In addition to a shorter review period, the fee supports the journal's continued operation and open-access publishing model. Standard submissions are always free. Submit Now » - Submit an Article to Inquiries Journal -
|