From Interstate - Journal of International Affairs VOL. 2015/2016 NO. 2Stuxnet: The World's First Cyber... Boomerang?
By
Interstate - Journal of International Affairs 2016, Vol. 2015/2016 No. 2 | pg. 1/1
IN THIS ARTICLE
KEYWORDS
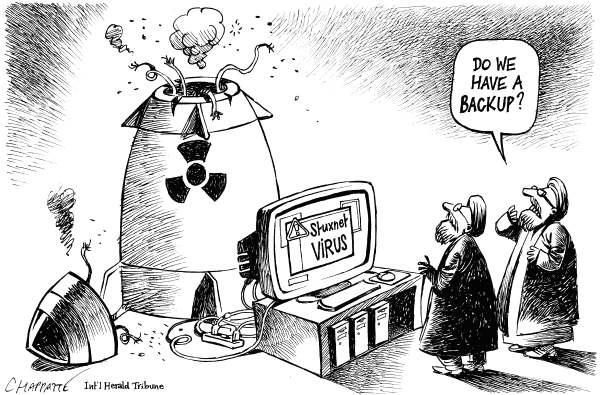
IntroductionIn June 2012, two years after the initial discovery of the Stuxnet worm,1 an excerpt from David Sanger's then soon to be released book entitled Confront and Conceal was published in the New York Times.2 This piece, purportedly based on the testimony of several current and former American, European and Israeli officials, declared that Stuxnet – "the world's first fully fledged cyber weapon"3 was engineered by the United States and Israel as part of a wider covert operation aimed at undermining the Iranian nuclear program.4 Whilst the United States and Israel had long been suspected of developing this complex piece of malware, Sanger described the nature of their involvement more fully than any previous account.5 Operation Olympic Games, the codename for this alleged joint venture, may well have succeeded in achieving its goal of disrupting Iran's nuclear enrichment program (although this debate is far from settled) but the deployment of a weaponized worm, which would cause physical damage to a nation-state's nuclear infrastructure, is likely to have spawned some rather sour implications for International Politics. It is these that this paper focuses on. This article argues that the release of the worm is likely to have: 1) fueled an on-going cyber arms race by demonstrating to other nations the strategic utility of cyber weapons; 2) elevated the severity of the cyber threat by providing a broad range of actors with a template from which to construct their own cyber weapons; 3) set a precedent for the use of cyber weapons as instruments of state policy. It should be noted that Sanger's account is far from definitive proof that the United States and Israel were the culprits behind the attacks on Iran's Natanz nuclear enrichment facility. However, regardless of who conducted the assault, the implications raised in this paper still apply given that Stuxnet unearthed itself in the summer of 2010. Stuxnet's Influence on the Cyber Arms RaceInterest and development in offensive cyber weapons programs certainly predates the release of Stuxnet. Even prior to its discovery in June 2010, U.S. intelligence officials had estimated there to be around twenty to thirty militaries with respectable offensive cyber capabilities.6 There is of course great difficulty in determining the precise period in which nations began to build-up their cyber arsenals as, in the words of Richard Clarke, former U.S. presidential advisor for cyber security, "the entire phenomenon of cyber war is shrouded in such government secrecy that it makes the Cold War look like a time of openness and transparency".7 Events such as the distributed denial of service (DDOS) attacks on Estonia and Georgia in 2007/2008, which saw their business, financial and media online communications severely hampered,8 demonstrated the strategic utility of cyberspace and thus would have intensified the emerging cyber arms race. Stuxnet, however, is widely regarded as a "game changer".9 Unlike the malware used in previous cyberattacks, it was highly targeted and designed to achieve a real world outcome.10 As Industrial Control System (ICS) security analyst Ralph Langner notes, rather than being designed for denial of service attacks or industrial espionage, "Stuxnet's goal was to physically destroy a military target not just metaphorically, but literally".11 This highly sophisticated worm was able to breach the air gap at Natanz and instruct cascades of bulky IR-1 centrifuges to spin into overdrive and self-destruct.12 This act, U.S. officials claim, would have set back Tehran's purported nuclear arms project by eighteen months to two years.13 The appeal of generating a Stuxnet-like cyber weapon for the implementation of state policy is then vast. The impact the release of this worm is likely to have had on the development and proliferation of cyber weapons worldwide should not be ignored. Not only are future variants of Stuxnet perfectly suited to covert operations because they afford their user a high degree of anonymity,14 (meaning that states need not be fearful of retaliation or international condemnation) but they are also low cost when compared to conventional weaponry15 and likely to possess tremendous asymmetric properties. But ownership of these future versions may not be limited to nation-states with ample resources. As the following section will demonstrate, Stuxnet is likely to have altered the nature of the cyber threat by inspiring and empowering a wide range of actors. Stuxnet: A Blueprint for Future Cyber WeaponsSean Collins and Stephen McCombie state that "Stuxnet and the future cyber weapons it will inspire have fundamentally changed the scope of cyber threats".16 Indeed, whilst the potential of cyber-attacks to be a significant threat to critical infrastructure had long been discussed, it was the discovery of this malware in 2010 that finally provided the proof of concept.17 Not only would this have been likely to inspire militaries to develop similar cyber weapons, but also a host of other actors including terrorist organizations, organized crime syndicates and hacktivist groups.18 Whilst there lacks concrete evidence to prove that it was the United States and Israel who engineered the worm, there exists little doubt as to the type of actor involved. As Claire Yorke, a cyber-security researcher at the think tank Chatham House, commented: Stuxnet's "sophistication and complexity suggests it would have required significant time and resources beyond the capability of non-state actors".19 The same, however, cannot be said today. Indeed, after Stuxnet "escaped into the wild" and infected thousands of machines on the public Internet, there are fears that the readily available malware will be reverse engineered not only by nation states for military purposes but also by other malicious actors who could then use the worm's code and structure as a blue print for designing their own cyber weapon.20 As Richard Clarke states in the appendix of the revised edition of Cyber War: "thanks apparently to U.S. intelligence, hackers around the world ha[ve] a sophisticated tool to attack the kind of networks that run electrical power grids, pipeline networks, railways, and manufacturing processes in refineries and chemical plants".21 "The best cyber weapon the United States has ever developed", he insists "it then gave to the world for free".22 Parties interested in replicating this potentially lethal cyber weapon may also be aided by the freely available analysis on it by security firms and anti-virus vendors such as Symantec, Kaspersky Labs and Langer Communications. Each have carefully dissected the malware and provided commentary on it. Whilst this information is of course highly valuable from a defensive standpoint, it could also, as Paulo Sharkarian has argued, be turned on its head and be used to provide inspiration, information and guidance for future cyber weapons development.23 The release of Stuxnet will have implications for all states reliant upon ICT; the U.S. itself is thus far from immune. Indeed, what the U.S. unleashed (assuming it was the U.S.) could well come back to bite them. Such fears occupy passages in a recent report sent to Congress. The document clearly expresses concern that Stuxnet could be adapted into a weapon that could be used to cause widespread damage to critical infrastructure located on U.S. soil.24 Clarke shares similar concerns; he even goes as far as to label Stuxnet a "cyber boomerang"a weapon that may one day come back around to hurt its original creators.25 Cyber Weapons as Instruments of State PolicySoon after the discovery of the malware in June 2010 speculation grew that this offensive cyber action would open the floodgates to newer, increasingly devastating digital attacks. The New Yorker's Steve Coll stated that Stuxnet "has established new and disturbing norms for state aggression on the Internet and its side-channels".26 Misha Glenny even went as far as to suggest that "all countries that possess an offensive cyber capability will be tempted to use it now that the first shot has been fired". Had Stuxnet been understood to be the work of a state like North Korea it might be interpreted by the international community as rogue behaviour, however with the U.S. as one the key architects, the use of cyber weapons leads to different conclusions. The role of the U.S. as a global leader with considerable power to set the agenda on issues of what is acceptable in terms of global conflict sets a precedent for future consideration of cyber weapons as a legitimate and effective tool of statecraft. Indeed, the non-violent nature of the attack may make it appear preferable to conventional kinetic weapons in some ways. In fact, there have been no follow up attacks on the scale of Stuxnet. However, given the long planning process for that project and the fact that it remained undetected for many years, this is not in itself indicative of anything conclusive. The important implications of U.S. involvement in Stuxnet remain in terms of the way the use of cyber weapons is perceived by the international community. Whether that is a positive development leading to less violent solutions to global tensions or a negative development leading to an increase in state-based attacks on critical infrastructure remains to be seen. ConclusionIt is quite clear that the goal of Stuxnet was to disrupt Iran's nuclear enrichment program. Regardless of whether this was part of a grander covert operation codenamed Olympic Games, the implications remain much the same. This paper has argued that the deployment of Stuxnet is likely to have: 1.) fueled an on-going cyber arms race by demonstrating to other nations the strategic utility of cyber weapons; 2.) elevated the nature of the cyber threat by not only providing evidence that well-guarded critical infrastructure could fall victim to a cyber-attack, but also because the malware and the analysis on it is readily available for a broad range of actors to access; and 3.) set a precedent, which contributes to the legitimization of cyber weapons as instruments of state policy. This highly sophisticated weaponized worm may have achieved its objective, but this is likely to have come at a cost; a cost which may in fact someday come back to harm its original creators. ReferencesBlanche, E. ‘Cyber wars'. The Middle East (London), December 2012. Clarke, R & Knake, R. Cyber War – The next threat to national security and what to do about it, 1st paperback edition (New York, HarperCollins Publishers, 2012). Coll, S. ‘Stuxnet and the Rewards (and Risks) of Cyber War'. The New Yorker (online), 7 June 2012. Available at http://www.newyorker.com/online/blogs/comment/2012/06/the-rewardsandrisks-of-cyberwar.html. Collins, S & McCombie, S. ‘Stuxnet: the emergence of a new cyber weapon and its implications', Journal of Policing, Intelligence and Counter Terrorism, 7:1, (2012) pp. 80-91. Farwell, J & Rohozinski, R. ‘Stuxnet and the Future of Cyber War', Survival: Global Politics and Strategy, 53:1 (2011), pp. 23-40. Glenny, M. ‘A Weapon We Can't Control'. The New York Times (online), 24 June 2012. Available at http://www.nytimes.com/2012/06/25/opinion/stuxnet-will-come-back-tohauntus.html. Hopkins, N. ‘Stuxnet attack forced Britain to rethink the cyber war'. The Guardian (online), 30 April 2011. Available at http://www.guardian.co.uk/politics/2011/may/30/stuxnet-attack-cyber-wariran. Hypponen, M. ‘Viewpoint: Stuxnet shifts the cyber arms race up a gear'. BBC News (online), 14 July 2012. Available at http://www.bbc.co.uk/news/technology-18825742. International Institute for Strategic Studies. ‘Stuxnet: targeting Iran's nuclear programme', Strategic Comments, 17:2 (2011) pp. 1-3. Langner, R. ‘Stuxnet: Dissecting a cyberwarfare weapon', IEEE Security & Privacy, 9 (2011) pp. 49-51. Rosenbaum, R. ‘Richard Clarke on Who Was Behind the Stuxnet Attack', Smithsonian Magazine (online), April 2012. Available at http://www.smithsonianmag.com/history-archaeology/Richard-Clarke-onWho-Was-Behind-the-Stuxnet-Attack.html. Sanger, D. ‘Obama Order Sped Up Wave of Cyberattacks Against Iran'. The New York Times (online), 1 June 2012. Available at http://www.nytimes.com/2012/06/01/world/middleeast/obama-orderedwaveof-cyberattacks-against-iran.html?pagewanted=all&_r=0. Shakarian, P. ‘Stuxnet: Cyberwar Revolution in Military Affairs', Small Wars Journal, 7:4 (2011), pp.1-10. Endnotes
Suggested Reading from Inquiries Journal
Inquiries Journal provides undergraduate and graduate students around the world a platform for the wide dissemination of academic work over a range of core disciplines. Representing the work of students from hundreds of institutions around the globe, Inquiries Journal's large database of academic articles is completely free. Learn more | Blog | Submit Latest in International Affairs |